The good news is - this is our first security notification in 9 years 🌟.
The bad news is - this is a security notification 😲.
TL;DR Summary 2021-001
1. Please Update to latest LTS
The key takeaway is that versions 8-11 of 2sxc have security issues; version 11 is especially vulnerable (and really easy to update). You should really update to the latest LTS - at the time of writing this is v11.22. You'll find a direct link in the download section.
2. Upgrade Process and Time Estimates
In most cases an upgrade can be completed in 5 minutes. But we recommend that you run an upgrade on a copy before upgrading your live environment, so depending on your setup it will take you longer to get a copy running for upgrade testing.
- If you have a typical website running 2sxc 11 you can expect it to just-work in just a few minutes.
- If you are updating from v10 it will usually just work, but there are some minor breaking changes. In most cases the error message will tell you exactly what you should do.
- If you are upgrading from V7+ or from a website that was originally created using V7 you'll probably still have some Razor templates which may use now unsupported APIs. 2sxc is really keen on stable APIs so in most cases it will work, or it will show you an error as to exactly what you should do. But in this scenario plan with 1-2 hours of upgrade work per portal.
- If you have custom DataSources from v8, v9 or v10 you'll need to update them. There is extensive new documentation as to how they work now, so it should be easy to do. Plan 1-2 hours per DataSource.
Note that our estimate time is pure developer time. If you need to make a customer quote you should at least double this estimate for PM and overhead. If it's your first upgrade ever estimate it 4x higher since the first time just takes longer.
For more details please check the breaking changes documentation.
Security Notification 2021-001
A few months ago the penetration tester burninatorsec discovered a security vulnerability in 2sxc. They contacted us and we were able to confirm the issue. Together we worked out a roadmap to first release another LTS before publishing the issue.
A big thanks to the burninatorsec for helping and giving us enough time to resolve the issue before creating a public announcement!
Everybody will usually want to know as much as possible to make a decision upgrade or not, yet the more we disclose, the more likely it would become that people would abuse it.
What is it?
It's a small issue - which can become a large issue.
The issue itself is fairly harmless, but as anybody with security experience will tell you - small issues can lead to suprisingly creative attack vectors. So small gaps will usually lead to something small being changed which will seem harmless until imperfect part of a system does something which will result in a larger hole which will then be used elevate the attackers grasp step-by-step.
So even if it's a small issue and has not been exploited in the wild, please assume that an attacker will be able to do a lot of damage - at least take the system down, possibly even extract data. If your DNN is older, he may even be able to capture the entire server and encrypt it.
Affected Versions
- v11.22 LTS is not affected
- 2sxc v8 till v11 are all affected
- 2sxc v11 releases have the highest risk - and they are the easiest to update
Non-Affected Versions or Mitigating Circumstances
- 2sxc releases before 8 are not affected according to our research
- If your DNN is not accessible on the internet (pure intranet use) it is not affected
- As of April 2021 we have no reports of this issue being abused
Stay Safe!
Love from Switzerland,
Daniel
PS: Don't panic 😉. This issue has never been abused as far as we know. But we take security really serious, which is why we're communicating this so strongly.
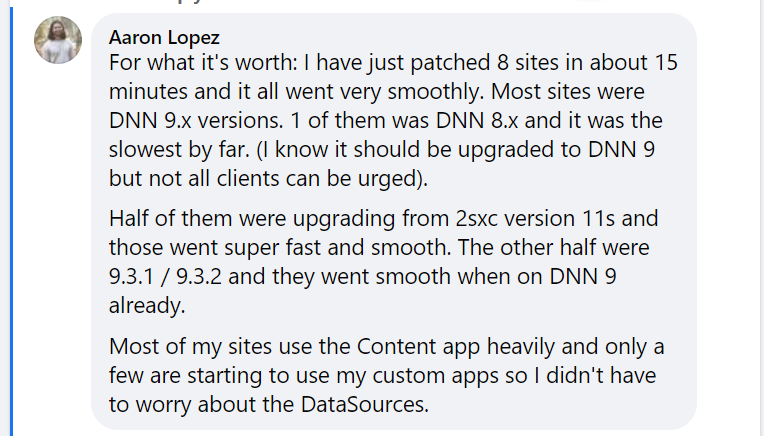
PPS: It's really not that hard - here's what Aaron wrote a few hours after we announced this: